A while ago, Microsoft warned about a critical issue with SMBv1. Microsoft also published updates for that Vulnerability.
The WannaCry Ransomware Attack used that Vulnerability in the SMBv1 implementation with an EternalBlue Exploit. I thing there is more to come! so my advice is to deploy critical updates as fast as possible, nothing new! And I told everyone to avoid the SMBv1 usage (by remove the support), like Microsoft did a few weeks ago.
Here is how to do that.
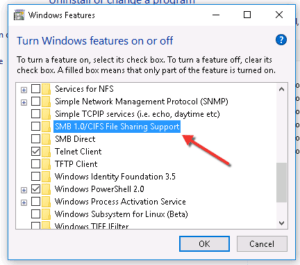 ][6]
][6]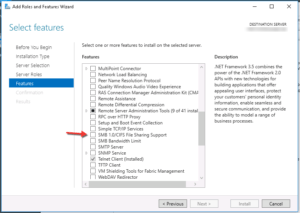 ][7]
][7]Another option: Use DSC to enforce the SMBv1 removal.
If you don’t have DSC (and ask yourself: Why not!!!) in place, you can use DSC local on your servers as well:
#requires -Version 4.0 -Modules PSDesiredStateConfiguration
<#
Work on any modern Microsoft Server OS
#>
# change this to any existing Path
$WorkPath = 'C:\scripts'
configuration RemoveSMB1
{
param ([string[]]
$ComputerName = 'localhost')
Import-DscResource -ModuleName PSDesiredStateConfiguration
Node $ComputerName {
# Removes SMBv1 support, if installed (enforced)
WindowsFeature 'SMB1' {
Name = 'FS-SMB1'
Ensure = 'Absent'
}
}
}
RemoveSMB1 -OutputPath $WorkPath
Start-DscConfiguration -Wait -Path $WorkPath
Here is the DSC MOF file (just an example):
Update: You can use a Group Policy for Clients and Servers. something I forgot to mention!
